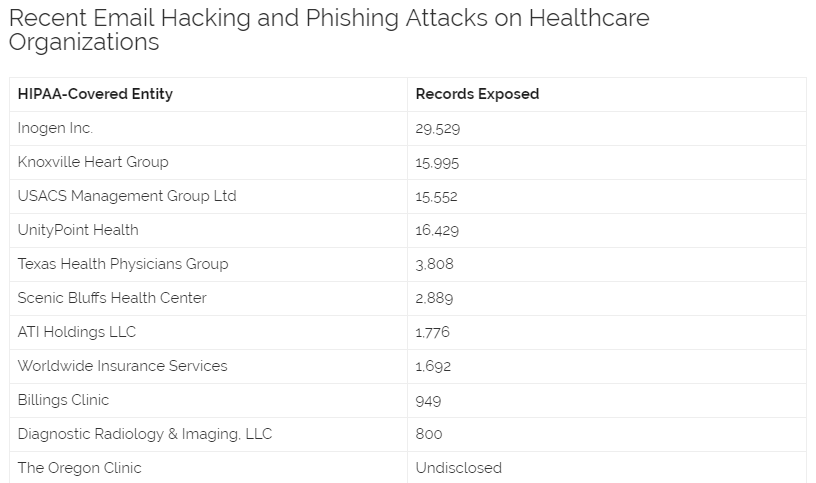
90,000 Records Compromised in Spate of Phishing Attacks on Healthcare Groups
The past few weeks have seen a massive increase in successful phishing attacks on healthcare groups. In a little over four weeks there have been 10 major email hacking incidents reported to the Department of Health and Human Services’ Office for Civil Rights (OCR), each of which has lead to the exposure and possible theft of over 500 healthcare records. Those ten incidents alone have seen almost 90,000 healthcare records impacted.
So far in 2018 there have been three data breaches involving the hacking of email accounts that have breached over 30,000 records. Agency for Health Care Administration experienced a 30,000-record breach in January, ATI Holdings, LLC was hit with a breach in March that resulted in the exposure of 35,136 records, and the biggest email hacking incident of the year impacted Onco360/CareMed Specialty Pharmacy and impacted 53,173 patients.
Wombat Security’s 2018 State of the Phish Report showed that quarters of groups experienced phishing attacks in 2017 and 53% suffered a focused attack. The Verizon 2017 Data Breach Investigations Report, released in May, revealed 43% of data breaches involved phishing, and a 2017 survey conducted by HIMSS Analytics on behalf of Mimecast revealed 78% of U.S healthcare providers have experienced a successful email-related cyberattack.
How Healthcare Groups Can Strengthen Phishing Defenses
Phishing targets the weakest link in an organizational chain: Staff. It therefore is logical that one of the best security measures against phishing is enhancing security awareness of employees and training the workforce how to recognize phishing efforts.
Security awareness training is obligatory under HIPAA (45 C.F.R. § 164.308(a)(5)(i)). All members of the workforce, including management, must be given training on security threats and the risk they pose to the group.
The OCR said in its July 2017 cybersecurity newsletter: “An organization’s training program should be an ongoing, evolving process and flexible enough to educate workforce members on new cybersecurity threats and how to respond to them”.
HIPAA does not state how often security awareness training should be conducted, although ongoing programs including a variety of training methods should be considered. OCR indicates many healthcare groups have opted for bi-annual training accompanied by monthly security updates and newsletters, although more regular training sessions may be appropriate depending on the level of risk faced by a group.
A combination of classroom-based classes, CBT training, newsletters, email alerts, posters, team talks, quizzes, and other training techniques can help a group develop a security culture and minimize susceptibility to phishing attacks.
The scope of threats is constantly changing. To keep up to date with new threats and scams, healthcare groups should consider signing up with threat intelligence services. Alerts about new techniques that are being used to spread malicious software and the latest social engineering ploys and phishing scams can be sent to employees to raise awareness of new threats.
Along with training, technological safeguards should be put in place to reduce risk. Advance antivirus solutions and anti-malware security measures should be deployed to identify the installation of malicious software, while intrusion detection systems can be used to quickly identify suspicious network activity.
Email security solutions including spam filters should be used to restrict the number of potentially malicious emails that are sent to end users’ inboxes. Solutions should monitor inbound email attachments using multiple AV engines, and be set up to quarantine emails containing possibly harmful file types.
Embedded URLs should be reviewed at the point when a user clicks. Effortss to access known malicious websites should be blocked and a review of unknown URLs should be performed before access to a webpage is allowed.
